United States Computer Emergency Readiness Team (US-CERT) has issued Alert TA14-300A – Phishing Campaign Linked with “Dyre” Banking Malware
Systems Affected: Microsoft Windows
United States Computer Emergency Readiness Team (US-CERT) has issued Alert TA14-300A – Phishing Campaign Linked with “Dyre” Banking Malware
Systems Affected: Microsoft Windows
Overview
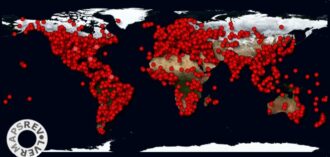
Since mid-October 2014, a phishing campaign has targeted a wide variety of recipients while employing the Dyre/Dyreza banking malware. Elements of this phishing campaign vary from target to target including senders, attachments, exploits, themes, and payload(s).[1][2] Although this campaign uses various tactics, the actor’s intent is to entice recipients into opening attachments and downloading malware.
Description
The Dyre banking malware specifically targets sensitive user account credentials. The malware has the ability to capture user login information and send the captured data to malicious actors.[3](link is external) Phishing emails used in this campaign often contain a weaponized PDF attachment which attempts to exploit vulnerabilities found in unpatched versions of Adobe Reader.[4](link is external)[5](link is external) After successful exploitation, a user's system will download Dyre banking malware. All of the major anti-virus vendors have successfully detected this malware prior to the release of this alert.[6](link is external)
Please note, the below listing of indicators does not represent all characteristics and indicators for this campaign.
Phishing Email Characteristics:
- Subject: "Unpaid invoic" (Spelling errors in the subject line are a characteristic of this campaign)
- Attachment: Invoice621785.pdf
System Level Indicators (upon successful exploitation):
- Copies itself under C:\Windows\[RandomName].exe
- Created a Service named "Google Update Service" by setting the following registry keys:
- HKLM\SYSTEM\CurrentControlSet\Services\googleupdate\ImagePath: "C:\WINDOWS\pfdOSwYjERDHrdV.exe"
- HKLM\SYSTEM\CurrentControlSet\Services\googleupdate\DisplayName: "Google Update Service"
Impact
A system infected with Dyre banking malware will attempt to harvest credentials for online services, including banking services.
Solution
Users and administrators are recommended to take the following preventive measures to protect their computer networks from phishing campaigns:
- Do not follow unsolicited web links in email. Refer to the Security Tip Avoiding Social Engineering and Phishing Attacks [7] for more information on social engineering attacks.
- Use caution when opening email attachments. For information on safely handling email attachments, see Recognizing and Avoiding Email Scams.[8]
- Follow safe practices when browsing the web. See Good Security Habits [9]and Safeguarding Your Data [10] for additional details.
- Maintain up-to-date anti-virus software.
- Keep your operating system and software up-to-date with the latest patches.
US-CERT collects phishing email messages and website locations so that we can help people avoid becoming victims of phishing scams.
You can report phishing to us by sending email to phishing-report@us-cert.gov.
References
- [1] MITRE Summary of CVE-2013-2729, accessed October 16, 2014
- [2] MITRE Summary of CVE-2010-0188, accessed October 16, 2014
- [3] New Banking Malware Dyreza, accessed October 16, 2014(link is external)
- [4] Adobe Security Updates Addressing CVE-2013-2729, accessed October 16, 2014(link is external)
- [5] Adobe Security Updates Addressing CVE-2010-0188, accessed October 16, 2014(link is external)
- [6] VirusTotal Analysis, accessed October 16, 2014(link is external)
- [7] US-CERT Security Tip (ST04-014) Avoiding Social Engineering and Phishing Attacks
- [8]US-CERT Recognizing and Avoiding Email Scams
- [9] US-CERT Security Tip (ST04-003) Good Security Habits
- [10] US-CERT Security Tip (ST06-008) Safeguarding Your Data
Revisions
October 27, 2014: Initial Release